Filter by
SubjectRequired
LanguageRequired
The language used throughout the course, in both instruction and assessments.
Learning ProductRequired
LevelRequired
DurationRequired
SkillsRequired
SubtitlesRequired
EducatorRequired
Results for "implementing data security and resource policies"

University of Michigan
Skills you'll gain: Pandas (Python Package), Jupyter, NumPy, Data Manipulation, Data Science, Data Analysis, Statistical Analysis, Pivot Tables And Charts, Data Cleansing, Data Import/Export, Probability & Statistics, Python Programming, Programming Principles

ISC2
Skills you'll gain: Network Security, Cybersecurity, Cyber Attacks, Infrastructure Security, Threat Detection, Computer Networking, Data Centers, General Networking, Network Planning And Design, Network Protocols, Network Model, Cloud Computing, TCP/IP
Johns Hopkins University
Skills you'll gain: Statistical Analysis, R Programming, Statistical Programming, Data Analysis, Debugging, Simulations, Program Development, Software Installation, Computer Programming, Data Structures, Performance Tuning, Data Import/Export

Cisco Learning and Certifications
Skills you'll gain: Cyber Threat Intelligence, Threat Detection, Workflow Management, Stakeholder Engagement, Cyber Operations, Cybersecurity, Stakeholder Management, Security Information and Event Management (SIEM), Incident Response, Security Management, Computer Security Incident Management, Cyber Attacks, Stakeholder Communications, Incident Management, Event Monitoring, Security Controls, Data Security, Customer Relationship Building, Network Security, Team Oriented

Royal Holloway, University of London
Skills you'll gain: Computer Security Incident Management, Cyber Governance, Incident Management, Incident Response, Security Management, Cyber Security Strategy, Cyber Security Policies, Human Factors (Security), Security Awareness, ISO/IEC 27001, Computer Security Awareness Training, Cyber Risk, Information Assurance
 Status: Free
Status: FreeThe State University of New York
Skills you'll gain: Cyber Threat Intelligence, Cyber Security Policies, Cybersecurity, International Relations, Cyber Risk, Cyber Operations, Cyber Governance, Infrastructure Security, Law, Regulation, and Compliance, Security Management, Political Sciences, Media and Communications, Computer Networking, Psychology

Skills you'll gain: Data Pipelines, Dataflow, Google Cloud Platform, Real Time Data, Data Lakes, MLOps (Machine Learning Operations), Dashboard, Data Warehousing, Extract, Transform, Load, Data Infrastructure, Cloud Storage, Big Data, Tensorflow, Unstructured Data, Data Integration, Data Processing, Data Visualization Software, Apache Hadoop, Applied Machine Learning, Apache Spark
 Status: Free
Status: FreeThe University of North Carolina at Chapel Hill
Skills you'll gain: Data Sharing, Data Management, File Management, Data Storage, Information Management, Metadata Management, Data Governance, Record Keeping, Data Security, Data Ethics, Information Privacy, Version Control

University of California San Diego
Skills you'll gain: Unit Testing, Data Structures, Development Testing, Java Programming, Software Testing, Performance Tuning, Debugging, Computer Programming, Algorithms, Object Oriented Programming (OOP), Theoretical Computer Science, Unstructured Data, Computer Science

University of California, Davis
Skills you'll gain: Data Governance, SQL, Data Quality, Query Languages, Data Manipulation, Data Modeling, Relational Databases, Data Science, Data Analysis, Database Management Systems, Descriptive Statistics

University of London
Skills you'll gain: Key Management, Security Management, Cyber Attacks, Cryptography, Cyber Security Policies, Cybersecurity, Encryption, Cyber Risk, Information Assurance, Security Controls, Incident Response
 Status: Free
Status: FreeCoursera Instructor Network
Skills you'll gain: Information Privacy, General Data Protection Regulation (GDPR), Personally Identifiable Information, Data Security, Data Governance, Data Ethics, Law, Regulation, and Compliance, Data Loss Prevention, Data Management, Security Controls, Regulatory Compliance, Compliance Management, Compliance Training, Data Sharing, Security Strategy, Regulatory Requirements, Data Processing, Risk Management, Employee Training, Risk Analysis
In summary, here are 10 of our most popular implementing data security and resource policies courses
- Introduction to Data Science in Python: University of Michigan
- Network Security: ISC2
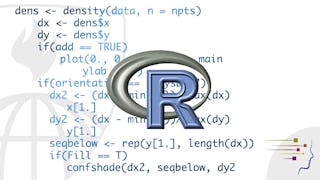
- R Programming: Johns Hopkins University
- Security Operations Center (SOC): Cisco Learning and Certifications
- Security Management and Governance: Royal Holloway, University of London
- International Cyber Conflicts: The State University of New York
- Data Engineering, Big Data, and Machine Learning on GCP: Google Cloud
- Research Data Management and Sharing: The University of North Carolina at Chapel Hill
- Data Structures and Performance: University of California San Diego
- SQL for Data Science: University of California, Davis










